
Introduction: Why HIPAA and GDPR Compliance Can't Rely on Patchwork Solutions
Healthcare organizations increasingly operate across both US and EU jurisdictions, making HIPAA and GDPR simultaneously applicable. Yet many still rely on policy-only frameworks that crumble under regulatory scrutiny or breach events. The French CNIL recently fined CEGEDIM Santé €800,000 for failing to implement technical measures preventing unauthorized data downloads. Documented policies without technical enforcement no longer satisfy regulators.
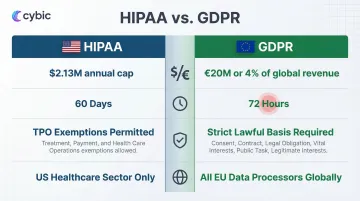
The challenge is structural. HIPAA and GDPR share fundamental goals, data protection and individual rights but diverge sharply in mechanism, scope, and enforcement. HIPAA allows 60 days for breach notification; GDPR demands 72 hours.
The consent requirements differ just as significantly. HIPAA permits broad data sharing for treatment, payment, and operations without explicit consent, while GDPR requires a specific lawful basis for every processing activity involving health data. Organizations subject to both can't simply layer policies on top of existing systems and hope for compliance.
This article explains what each regulation requires, where they align and diverge, the four pillars of compliant data governance, and the technical and organizational steps to build a durable program that satisfies both frameworks without duplication or conflict.
TLDR:
- HIPAA and GDPR impose conflicting timelines: 72 hours vs. 60 days for breach notification
- GDPR fines reach €20 million or 4% of global revenue; HIPAA caps at $2.1M annually per violation category
- Dual compliance rests on four pillars: data discovery, access control, data quality, and policy enforcement
- Technical safeguards must be embedded architecturally, not bolted on post-deployment
- GDPR and the EU AI Act now mandate AI governance frameworks for health data processing
HIPAA and GDPR: What They Require and Who They Apply To
What HIPAA Governs and Who Must Comply
HIPAA is a US federal law covering covered entities such as healthcare providers, insurers, and clearinghouses and their business associates that create, receive, maintain, or transmit protected health information (PHI) and electronic PHI (ePHI). Since 2003, HHS OCR has received over 374,321 complaints and imposed civil money penalties in 152 cases, totaling $144.9 million.
HIPAA's three core rules:
- Privacy Rule: Governs permissible uses and disclosures of PHI, including treatment, payment, and healthcare operations (TPO) exemptions
- Security Rule: Mandates administrative, physical, and technical safeguards for ePHI
- Breach Notification Rule: Requires notification to affected individuals and HHS within 60 days of breach discovery
The HITECH Act (2009) extended liability to business associates, increased penalties, and tightened security requirements for electronic health records. Business associates are now directly liable for HIPAA violations, including failures to provide breach notification or comply with the Security Rule.
2024/2025 HIPAA Penalty Tiers:
| Culpability Tier | Per-Violation Range | Annual Cap |
|---|---|---|
| Tier 1: Lack of Knowledge | $141 – $71,162 | $2,134,831 |
| Tier 2: Reasonable Cause | $1,424 – $71,162 | $2,134,831 |
| Tier 3: Willful Neglect (Corrected) | $14,232 – $71,162 | $2,134,831 |
| Tier 4: Willful Neglect (Uncorrected) | $71,162 – $2,134,831 | $2,134,831 |
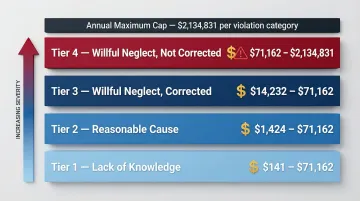
Source: 45 CFR Part 102 inflation adjustments effective August 8, 2024
What GDPR Governs and Who Must Comply
HIPAA defines your obligations within the US healthcare system. GDPR extends compliance requirements across borders. Any organization processing personal data of EU/EEA residents falls under GDPR, regardless of where that organization is headquartered. A US healthcare company with European patients or employees must satisfy both frameworks simultaneously.
Key GDPR obligations:
- Lawful basis for processing: Every data processing activity requires a specific legal justification under Articles 6 and 9
- Health data is a "special category" under Article 9, requiring explicit consent and heightened protections beyond standard personal data
- Data subjects hold rights to access, erasure, portability, and rectification broader than HIPAA's individual rights framework
- Organizations running large-scale processing of special category data must appoint a Data Protection Officer (DPO)
- High-risk processing activities trigger mandatory Data Protection Impact Assessments (DPIAs) under Article 35
GDPR mandates breach notification to supervisory authorities within 72 hours of becoming aware of a breach. Maximum fines reach €20 million or 4% of total worldwide annual turnover, whichever is higher. For large enterprises, that 4% figure can dwarf even the highest HIPAA annual caps by orders of magnitude.
Where HIPAA and GDPR Overlap and Where They Diverge
Shared Principles: Where Both Frameworks Align
Both regulations require:
- Purpose limitation: Data used only for stated purposes
- Security safeguards: Encryption, access controls, and audit capabilities
- Individual rights: Access to personal health data within defined timeframes
- Breach notification: Mandatory reporting when breaches occur
Organizations that satisfy both can build on a common governance foundation. That shared emphasis on individual rights creates natural alignment. Where the frameworks start to split, however, the gaps carry real compliance risk and ignoring them is where dual-jurisdiction programs typically break down.
Key Divergences Organizations Must Understand
Three fault lines define where HIPAA and GDPR conflict most sharply:
The consent collision: HIPAA permits covered entities to use PHI for treatment, payment, and operations (TPO) without patient authorization. GDPR requires a specific lawful basis for each processing activity involving health data. Dual-compliance programs must account for this fundamental gap: what's permissible under HIPAA may still violate GDPR. GDPR also grants individuals a "right to be forgotten" with no direct HIPAA equivalent, creating another point of friction.
Geographic and sectoral scope: HIPAA is US-specific and healthcare-sector-specific. GDPR is geographically broad and sector-agnostic. An organization subject to both cannot simply apply HIPAA standards and assume GDPR compliance. For overlapping obligations, the stricter GDPR standard generally controls organizations cannot satisfy GDPR by meeting HIPAA alone.
Penalties divergence: Simultaneous violations compound financial and reputational exposure. A breach affecting both US patients and EU residents triggers both penalty frameworks: potentially $2.1M under HIPAA plus up to €20M or 4% of global revenue under GDPR. The combined exposure makes dual-framework gaps a boardroom-level risk, not just a compliance footnote.
| Framework | Maximum Penalty | Breach Timeline | Consent Model |
|---|---|---|---|
| HIPAA | $2,134,831 annual cap per category | 60 days | TPO exemptions allow processing without authorization |
| GDPR | €20M or 4% global turnover | 72 hours | Strict lawful basis required for all processing |
The 4 Pillars of Data Governance for HIPAA and GDPR Compliance
These four pillars define how compliant organizations structure their data governance programs drawn from frameworks like DAMA-DMBOK and validated by what regulators actually audit.
Pillar 1: Data Discovery and Classification
Neither HIPAA nor GDPR compliance can begin without knowing what data exists, where it lives, and how it flows. Data cataloging and automated classification of PHI and PII are prerequisites for every downstream governance activity. Organizations must identify:
- All systems storing or processing health data
- Data flows between systems, vendors, and jurisdictions
- Classification tags for PHI, ePHI, and GDPR special category data
- Retention requirements and deletion schedules
Gaps in discovery turn breach investigations into guesswork and regulators don't accept guesswork as a timeline for data subject access requests.
Pillar 2: Access Control and Data Stewardship
Role-based access controls (RBAC), least-privilege principles, and assigned data stewards ensure sensitive health data is accessible only by authorized individuals. This satisfies both HIPAA's technical safeguard requirements and GDPR's security obligations under Article 32.
Key components:
- Unique user identification and authentication
- Multi-factor authentication for ePHI access
- Automatic logoff and session management
- Regular access reviews and privilege audits
- Named data stewards accountable for specific data domains
Pillar 3: Data Quality and Lineage
Accurate, traceable data is required for compliance audits, breach investigations, and data subject access requests. Lineage tracking knowing data's source, transformations, and destinations enables organizations to:
- Respond to regulatory inquiries with documented evidence
- Identify the full scope of a breach across systems
- Validate data accuracy for clinical decision-making
- Trace data flows for cross-border transfer compliance
Healthcare breaches average $10.93 million, the highest of any industry for 13 consecutive years making accurate lineage critical for damage control. making accurate lineage critical for damage control. That same traceability is what Pillar 4 builds on: turning documented data flows into enforceable, auditable policy.
Pillar 4: Policy Enforcement and Auditability
Documented policies, automated enforcement, and comprehensive audit logs create the accountability layer both regulations demand. This includes:
- Evidence of consent and lawful basis documentation
- Access records showing who viewed or modified PHI
- Incident response timelines for breach notification
- Audit trails regulators will request during investigations
During investigations, regulators don't review policy documents in isolation, they pull audit logs, access records, and breach timelines. If technical enforcement isn't generating that evidence automatically, written policies offer little protection.

Technical Safeguards: Building a Compliant Data Architecture
HIPAA's Security Rule requires three categories of safeguards:
- Administrative: Workforce training, risk assessments, information system activity review
- Physical: Facility access controls, device and media disposal
- Technical: Unique user identification, encryption, audit controls
GDPR Article 32 similarly requires "appropriate technical and organizational measures," including pseudonymization, encryption, and regular testing of security effectiveness.
Non-negotiables for compliant architecture:
- End-to-end encryption of data at rest and in transit
- Multi-factor authentication for all ePHI access
- Automated audit logging with tamper-resistant storage
- Data masking or de-identification for secondary use
- Regular penetration testing and vulnerability assessments
EDPB case digests highlight common failures: unencrypted backup databases, transmission via unencrypted HTTP or email, and passwords stored in plain text. These technical failures trigger enforcement even when policies exist on paper.
Cross-Border Data Transfers
Enforcement risk compounds when data crosses borders. The European Commission adopted an adequacy decision for the EU-U.S. Data Privacy Framework on July 10, 2023, allowing data to flow to participating US organizations without additional safeguards. Organizations not certified under the framework must rely on Standard Contractual Clauses (SCCs) or other approved transfer mechanisms, each carrying its own documentation and audit requirements.
Platforms like Cybic's Drava address this by embedding access controls, encryption, and audit logging directly into the data platform architecture. Security controls are configured at the infrastructure layer, which prevents them from being bypassed or inconsistently applied as data pipelines scale or change.
Implementing a HIPAA and GDPR Data Governance Program
Organizational Structure
Start by establishing a cross-functional Data Governance Council. This group sets policy, resolves conflicts between regulatory requirements, and owns accountability across the organization. Core representation should include:
- Compliance and legal : policy ownership and regulatory interpretation
- IT and security : technical controls and system access
- Clinical or operational leadership : business context and workflow alignment
- DPO (where GDPR mandates one) and HIPAA Security/Privacy Officer : regulatory accountability
Implementation Sequence
Conduct data inventory and risk assessment
- Map all PHI and PII flows across systems and vendors
- Identify gaps between current state and regulatory requirements
- Document findings per HIPAA risk analysis requirements and GDPR DPIA standards
Draft and enforce data governance policies
- Align policies to both HIPAA and GDPR requirements
- Define roles, responsibilities, and escalation procedures
- Establish consent management and lawful basis documentation
Implement technical controls
- Deploy encryption, RBAC, and audit logging
- Test controls through penetration testing and access reviews
- Automate policy enforcement where possible
Establish breach response workflow
- Define timelines for both HIPAA (60 days) and GDPR (72 hours)
- Create notification templates for regulators and individuals
- Assign incident response roles and communication protocols

Vendor and Business Associate Management
The implementation steps above address internal controls but your exposure doesn't stop at your own systems. Both HIPAA Business Associate Agreements (BAAs) and GDPR Data Processing Agreements (DPAs) require formal contracts with third-party processors. A compliant governance program includes:
- Vendor risk assessment and due diligence
- Contractual requirements for safeguards and breach notification
- Ongoing monitoring and audit rights
- Subcontractor management and approval processes
Breaches involving business associates or vendors accounted for 30% of all incidents, a figure that doubled in a single year. Without active vendor governance, organizations inherit third-party risk they often don't detect until a breach occurs.
The Role of AI in Modern Data Governance
AI-powered tools transform data governance at scale. Automated data classification, anomaly detection for potential breaches, policy compliance monitoring, and intelligent audit trail generation reduce manual overhead across large, complex data environments. AI adoption in healthcare reached 85% by the end of 2024.
Responsible AI considerations: Deploying AI on healthcare data creates governance obligations. Organizations must ensure:
- AI models don't perpetuate bias in clinical decisions
- AI-driven actions are auditable and explainable
- No proprietary or patient data trains third-party models without authorization
- Data Protection Impact Assessments (DPIAs) are completed for AI systems processing health data
Two regulatory frameworks set the compliance floor for AI in healthcare settings:
- The EU AI Act (in force August 1, 2024) classifies medical software as high-risk, mandating risk mitigation, high-quality training datasets, and human oversight
- HHS Section 1557 guidance prohibits discrimination through patient care decision support tools
Meeting these obligations requires governance embedded at the architecture level, not added after deployment. Cybic's governed AI automation platform builds RBAC, encrypted data protection, and full auditability directly into AI workflows, so compliance is structural rather than retrofitted.
AI handles the repetitive work classification, anomaly detection, audit log generation but it doesn't replace human judgment. Policy design, risk assessments, and breach response decisions still require people accountable to the organization. Governance councils set the rules; AI enforces them at scale.
Frequently Asked Questions
What are the 4 pillars of data governance?
The four pillars are data discovery and classification, access control and data stewardship, data quality and lineage, and policy enforcement and auditability. These pillars work together to support compliant, auditable data management under both HIPAA and GDPR.
Will AI replace data governance?
No. AI automates and enhances data governance tasks such as classification, monitoring, and anomaly detection, but cannot replace human-led policy design, organizational accountability, and the regulatory judgment that frameworks like HIPAA and GDPR require.
What is the difference between HIPAA and GDPR?
HIPAA is a US law specific to healthcare entities protecting PHI, while GDPR is an EU regulation applying to any organization processing personal data of EU residents regardless of sector or location. GDPR has broader individual rights, stricter consent requirements, and far higher financial penalties.
Can an organization be subject to both HIPAA and GDPR simultaneously?
Yes. A US healthcare provider or health tech company handling data of EU residents whether patients or employees must comply with both regulations. This requires a unified governance approach that satisfies the stricter standard where the two frameworks overlap.
What are the penalties for HIPAA and GDPR violations?
HIPAA penalties range from $141 to $71,162 per violation, with an annual cap of $2,134,831 per violation category. GDPR fines reach up to €20 million or 4% of global annual turnover, whichever is higher.